Your Vulnerability Age Filter Is a Security Liability
.png)
Deprioritizing old CVEs used to be a defensible shortcut.
AI just made it a liability.
Security teams have too many CVEs and not enough people. Shortcuts emerge.
One of the most common is recency bias: prioritize the newest vulnerabilities and deprioritize the rest. Not because older issues are safe, but because teams need a way to manage overload.
That logic made sense when weaponizing an old vulnerability required real expertise, access to exploit markets, and meaningful development time.
That world no longer exists.
AI Has Turned Exploit Development into a Commodity Workflow
In August 2025, researchers demonstrated an AI pipeline that generates working, validated exploits for published CVEs in 10 to 15 minutes, at roughly $1 per exploit. This is not a point innovation, it’s a structural shift in attacker economics. Exploit development is no longer a bottleneck.
The system ingests CVE advisories and patch data, builds vulnerable test environments, generates proof-of-concept code, and validates results, without a human in the loop. There are 130-plus new CVEs published every day. An attacker running this at scale can systematically work through years of deprioritized backlog over a weekend. Attackers don't need to limit themselves to new vulnerabilities. The old ones are just as viable.
Systems like Claude Mythos under Project Glasswing reinforce the same direction: large-scale vulnerability discovery and exploitation reasoning is becoming automated, fast, and scalable.
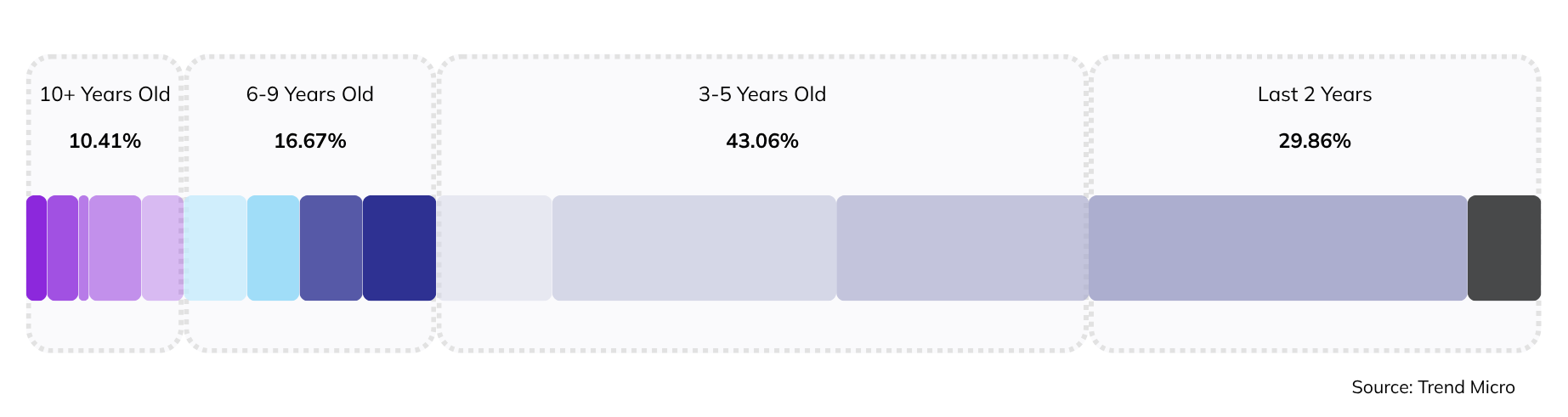
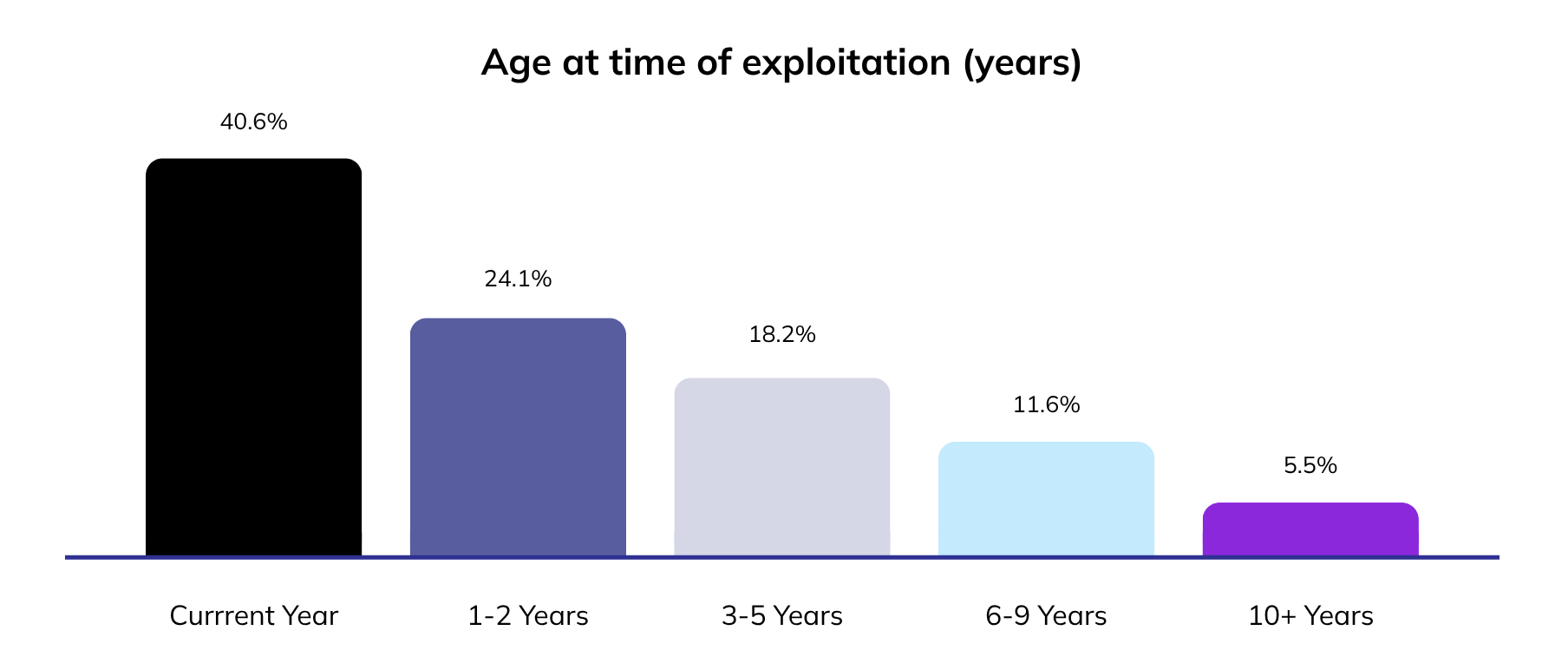
Research from Trend Micro found that over 70% of exploit requests on criminal underground forums were for vulnerabilities more than two years old. Almost 10% of targeted flaws between 10-15 years old. CVE-2011-2688, a SQL injection flaw from 2011, was actively used by FinStealer malware to target banking institutions. In 2025, unidentified threat actors compromised Microsoft Exchange servers across 26 countries by exploiting a cluster of Exchange vulnerabilities from 2021 (including CVE-2021-26855), years after patches were available, because enough organizations never applied them.
Age is not a proxy for safety. It is a proxy for how long an attacker has had to find a way in.
And when exploit development costs $1 and takes 15 minutes, the exploitation curve doesn't care how old the vulnerability is. It compounds with neglect.
The Numbers Are Worth Sitting With
CISA added 245 vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog in 2025, a 30% jump above the prior trend. More significantly, older vulnerabilities newly added to that list grew nearly 45% year over year. The oldest entry added in 2025 was CVE-2007-0671, an 18-year-old Microsoft Office remote code execution flaw.
These are not edge cases. These are vulnerabilities being actively exploited in production environments today.
At the same time, the pace of exploitation is accelerating. Rapid7 observed a 105% year-over-year increase in confirmed exploitation of newly disclosed high-severity vulnerabilities. Google Cloud's Threat Horizons H1 2026 report also found that the median time from disclosure to active exploitation has collapsed from weeks to days.
In some cases, it is measured in hours. In activity attributed to Storm-1175, the time from initial access to data exfiltration and ransomware deployment was under 24 hours. That's the window your backlog has to survive.
Put those two trends together: the exploitation window is shrinking for vulnerabilities, and AI is reopening the window on every old vulnerability you decided wasn't worth fixing.
The backlog is no longer a passive risk. It is an active attack surface.
CVSS is an Incomplete Signal, Recency is a Dangerous One
CVSS scores don't update when threat context changes. A vulnerability scored 7.8 in 2020 still shows as 7.8 today, even if working exploit code is now circulating in criminal forums and the flaw has been incorporated into active ransomware toolkits. CVSS measures theoretical severity. It says nothing about whether attackers are targeting it in the wild, whether your specific environment is reachable, or whether the exploitation window has reopened.
Age compounds the problem. Prioritizing by recency made sense as a triage shortcut when weaponizing an old vulnerability required real expertise and development time. That calculus no longer holds. Now it's a systematic blind spot. Attackers know it exists. AI-assisted scanning pipelines are built to exploit it.
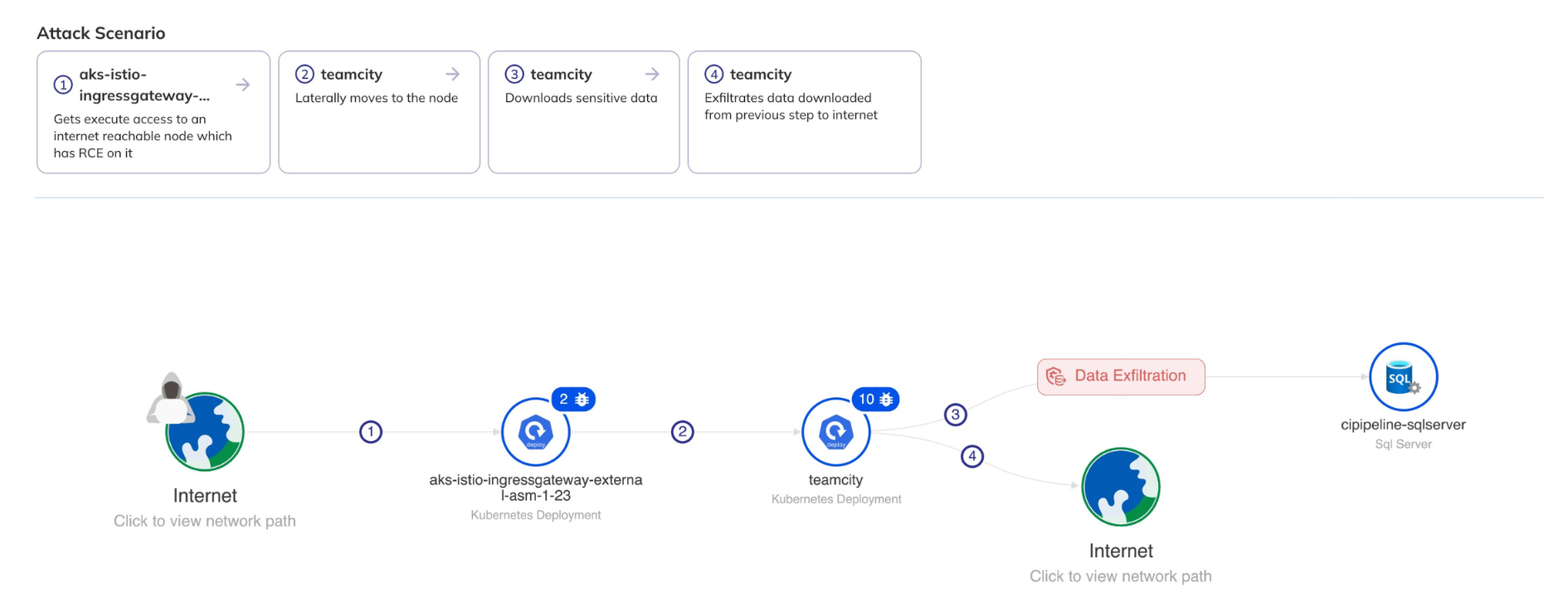
The right question is not how old a CVE is. It's whether there's a viable attack path to it in your specific environment, and whether active exploit capability exists. A CVSS 9.5 from 2022 with no reachable path and no known exploitation is genuinely low priority. A CVSS 6.5 from 2019 sitting in front of an exposed service, chained with an over-permissioned IAM role, is not.
Related: When Permissions Become the Attack Surface: Identity and Entitlement Risk in Cloud Security
Attackers don't target CVEs. They target systems, chaining whatever combination of vulnerabilities, misconfigurations, and permission gaps gets them to their objective. A CVE score evaluated in isolation, or filtered by age, doesn't reflect that reality.
Better Prioritization Is the Prerequisite. It's Not the Finish Line
If age is not a valid filter, and severity is incomplete, then prioritization has to be grounded in something else: exploitability in your specific environment.
That shift sounds straightforward. In practice, it is where most programs break.
Getting to exploitability-based prioritization requires correlating CVEs with asset inventory, understanding reachability, and mapping how vulnerabilities combine with misconfigurations and permissions to form attack chains. Most tools don’t do this natively. Most teams don’t have the time to do it manually at scale.
As a result, most programs fall back to approximations. CVSS, EPSS, or vendor-enriched scoring models. Each step is an improvement, but they still describe how dangerous a vulnerability is in general, not whether it is actually exploitable in your environment.
Even when teams identify what actually matters, they still cannot move fast enough to fix it.
Security identifies the right issues. They are handed to engineering as tickets. Priority is debated. Fixes compete with other work. By the time it ships, the window that mattered has already closed, or worse, been exploited.
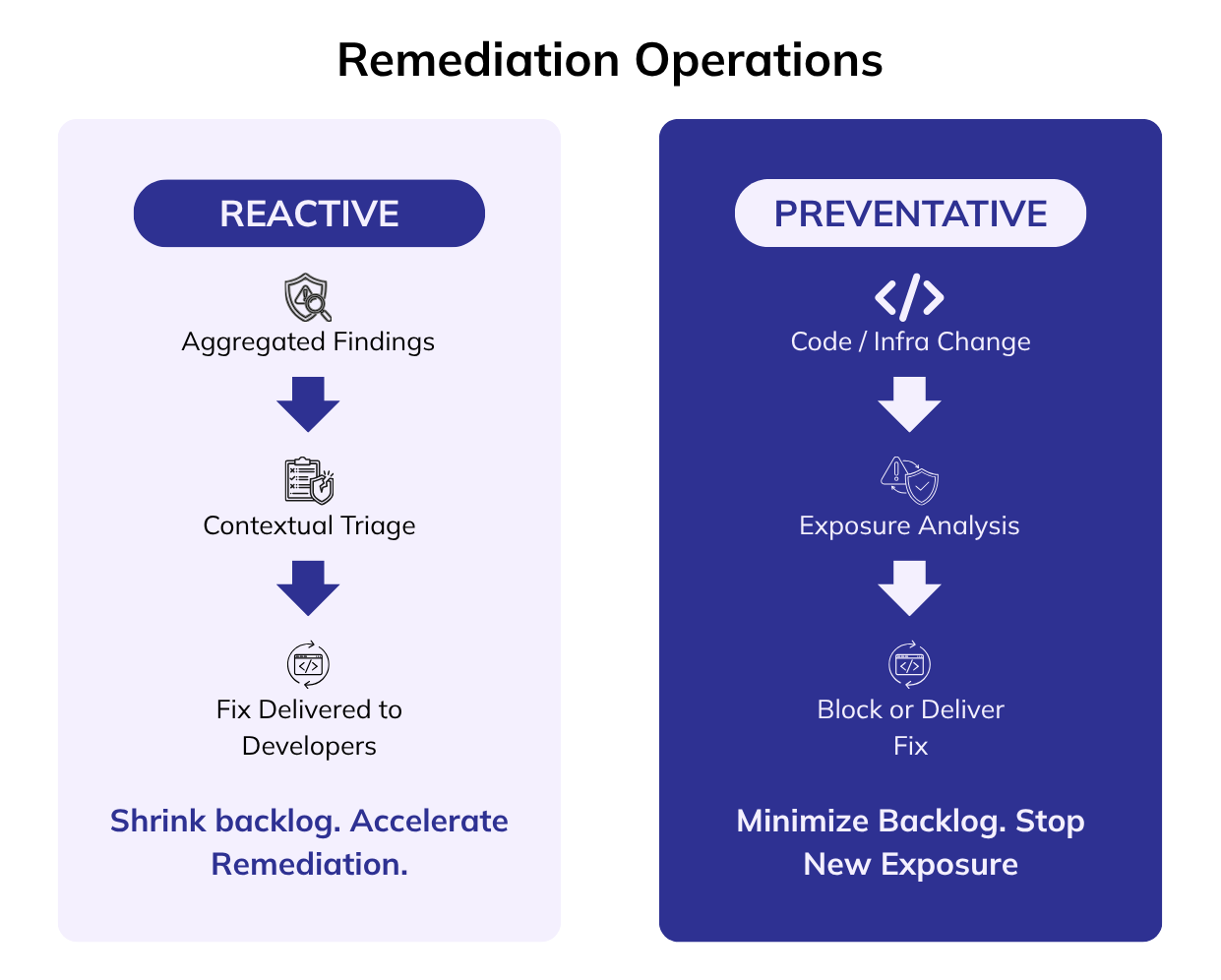
The discipline that addresses this is Remediation Operations: the operational layer between finding and fix. It takes environment-specific context, determines what is actually exploitable, and drives those issues through to verified remediation at a speed that matches the threat landscape
Related: Vulnerability Remediation: Down and Up We Go
Keeping up with the speed and scale of vulnerabilities requires two modes of operation:
The first is reactive: working on existing backlog to compress the time between a finding being identified and a developer having a validated, context-aware fix. This is where most exposure lives today.
The second is preventative: eliminating new exposures from becoming backlog by analyzing changes to code, infrastructure, and configuration before they reach production to determine whether they introduce new exploitable conditions or attack chains. High-risk changes are blocked or mitigated early. Low-risk changes move without friction.
Related: Preventing Exposure Before It Becomes Backlog: Introducing Averlon Precog
The organizations that manage this well are not patching everything faster. They’re patching the right things faster, and ensuring that what remains does not form viable attack pathways.
Where This Leaves Your Program
The pattern across 2025 data is consistent:
- Over 70% of criminal forum exploit requests target CVEs more than two years old.
- AI has compressed exploit development to under 15 minutes at roughly $1 per exploit.
- Older vulnerabilities added to CISA's active exploitation list grew nearly 45% in 2025.
More broadly, software vulnerability exploitation has overtaken stolen credentials as the leading cloud initial access vector.
If your prioritization workflow uses age as a filter, you have a systematic blind spot. Attackers know it exists. AI-assisted tooling is making it cheaper and faster to exploit.
Exploitability in your specific environment is the only signal that holds up under these conditions. Getting from that signal to a verified fix, faster than attackers can move, is what a modern remediation operations program has to deliver.
Old does not mean safe.
It means the clock has been running longer than you thought.
Most programs are optimized for managing backlog. Attackers are optimized for exploiting it.
* * *
Averlon is a remediation operations platform that helps security teams move from vulnerability findings to verified fixes. Exploitability analysis, attack chain context, and agentic remediation, built to compress the time between discovery and remediation.
Learn more at averlon.ai.
Featured Blog Posts
Explore our latest blog posts on cybersecurity vulnerabilities.
Ready to Reduce Cloud Security Noise and Act Faster?
Discover the power of Averlon’s AI-driven insights. Identify and prioritize real threats faster and drive a swift, targeted response to regain control of your cloud. Shrink the time to resolution for critical risk by up to 90%.





.png)