Enterprises Reducing Real Exposure with Averlon












Finding Doesn't Shrink Risk. Fixing Does.
Vulnerabilities keep rising - 28,000 in 2023, 48,000+ in 2025. Finding more isn't sustainable. Attackers move in days. Remediation often takes months.
This Exposure Window, the time between finding and fixing, is the real risk.
Closing it is not about finding more. It is about fixing what actually matters.
5 Days
Median time from disclosure to exploit. Attackers move almost immediately.

80% Unpatched
Vulnerabilities still open 30 days after patch release.

200+ Days
Average time it takes organizations to remediate vulnerabilities.

Meet Averlon
The Agentic Remediation Operations platform closing your Exposure Window.
Most tools generate findings and severity scores.
Averlon determines what is materially exploitable in your environment and delivers safe fixes directly into developer workflows.
It applies the same reasoning pre-merge, preventing new exposure before it becomes backlog.
Exposures get closed. Backlogs shrink. Risk is reduced.

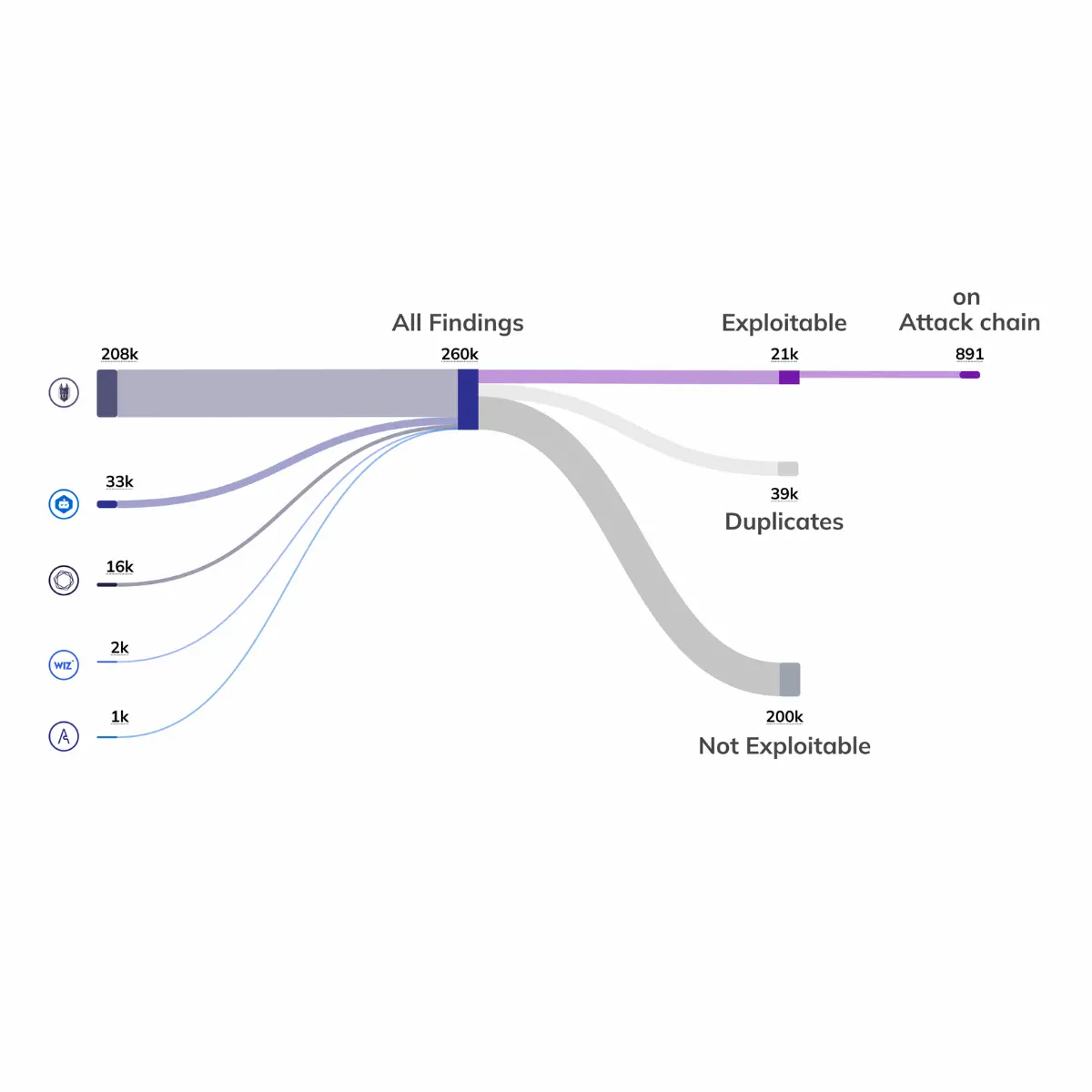
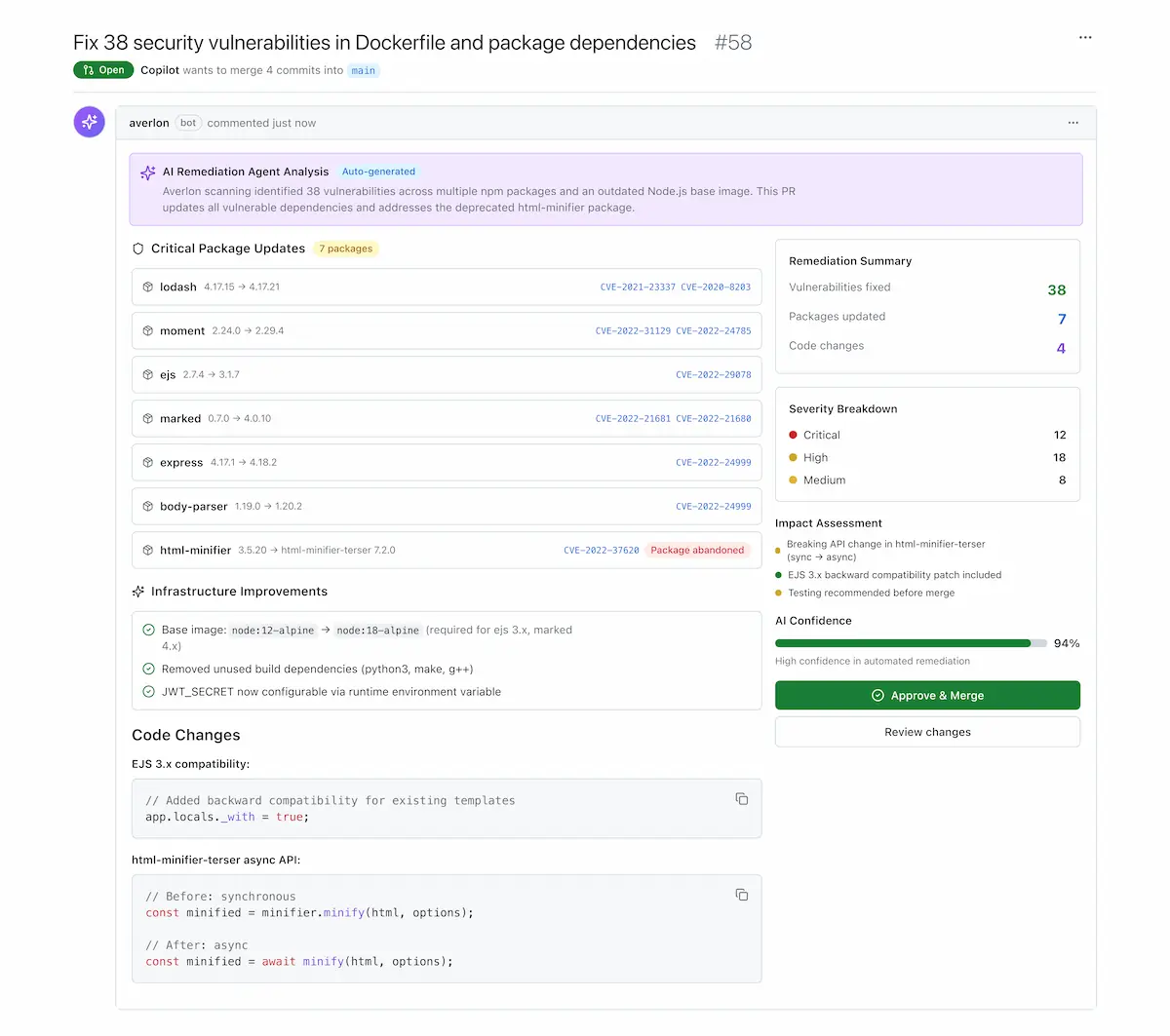
Accelerate Fixes, Prevent Exposure
Delivers safe, context-aware fixes directly within IDEs, source control systems, and CLI, and applies the same reasoning pre-merge to prevent new exposure from entering production.
Prioritize Fixes That Matter
Determines which exposures are materially exploitable in your environment and prioritizes fixes that break attack chains across identity, network, and configuration.
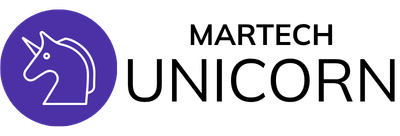
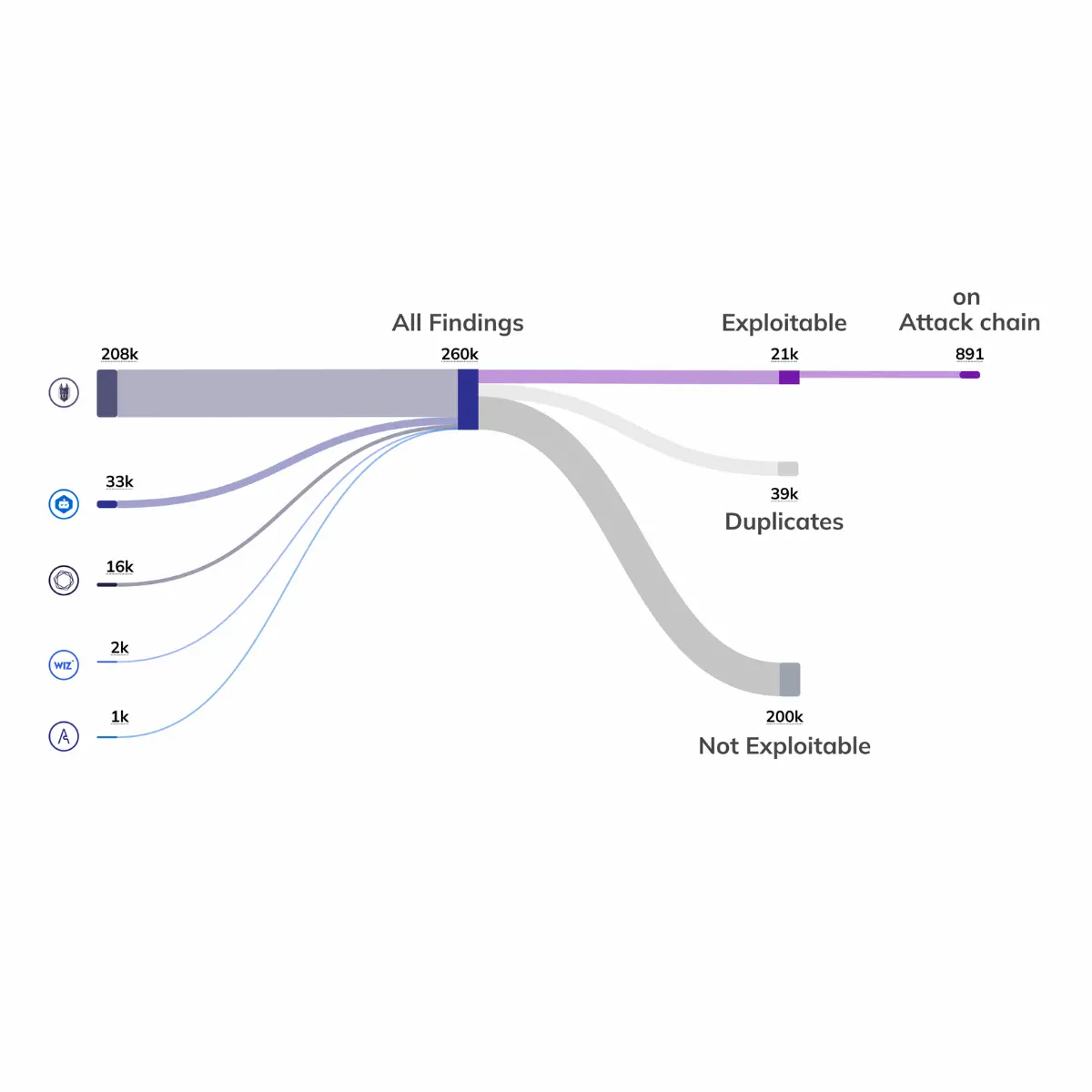
Eliminate Backlog Noise
Eliminates non-exploitable findings through environmental reasoning, reducing manual triage load and focusing teams on defensible remediation decisions.
Remediation at a Different Speed.
Less noise. Faster fixes. Measurable exposure reduction.
Faster remediation of critical exposures
Reduction in false positives, reducing burnout and backlogs
Rise in remediation velocity — from 200+ days to minutes
What Sets Averlon Apart?
Most security tools focus on visibility. They surface findings and assign severity.
Visibility alone doesn't reduce risk. Action does.
Averlon is built to turn visibility into action. To close the Exposure Window, the gap between a finding and a fix.
Focus On What is Actually Exploitable
Most findings don't matter in your environment.
Averlon determines what is applicable and reachable, identifying the exposures that are materially exploitable and eliminating backlog noise.
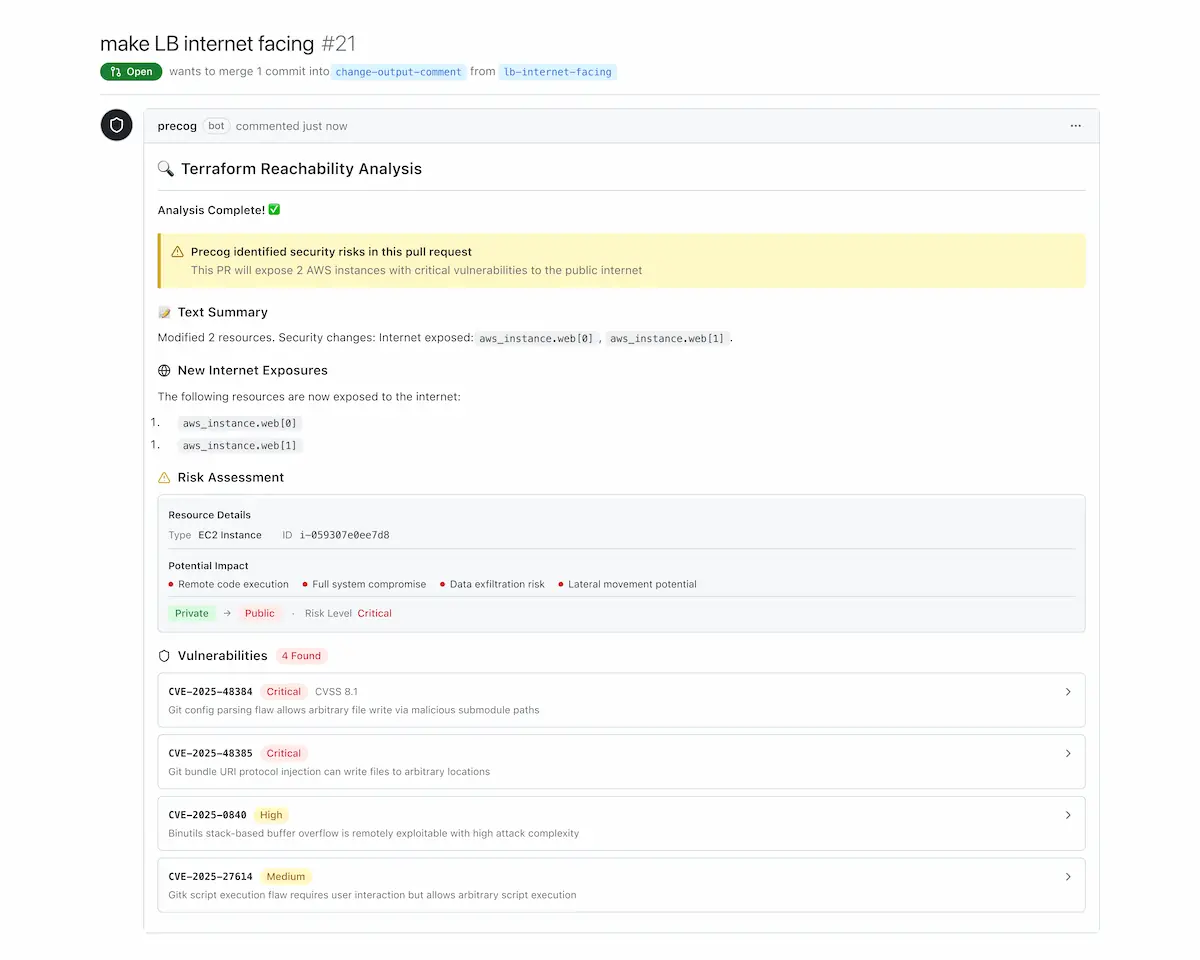
Break Attack Chains to High-Value Assets
Once noise is removed, the goal is to focus on what matters.
Averlon models how vulnerabilities, misconfigurations, identity, and permissions combine to reach critical data, and prioritizes fixes that break those chains.

Deliver Fixes That Can Be Applied Safely
Fixing is slow, risky, and competes with innovation. It's often handled by developers whose primary focus isn't security.
Averlon delivers context-aware fixes at the right layer, accounts for breaking changes, and integrates directly into developer workflows so fixes can be applied safely and quickly.
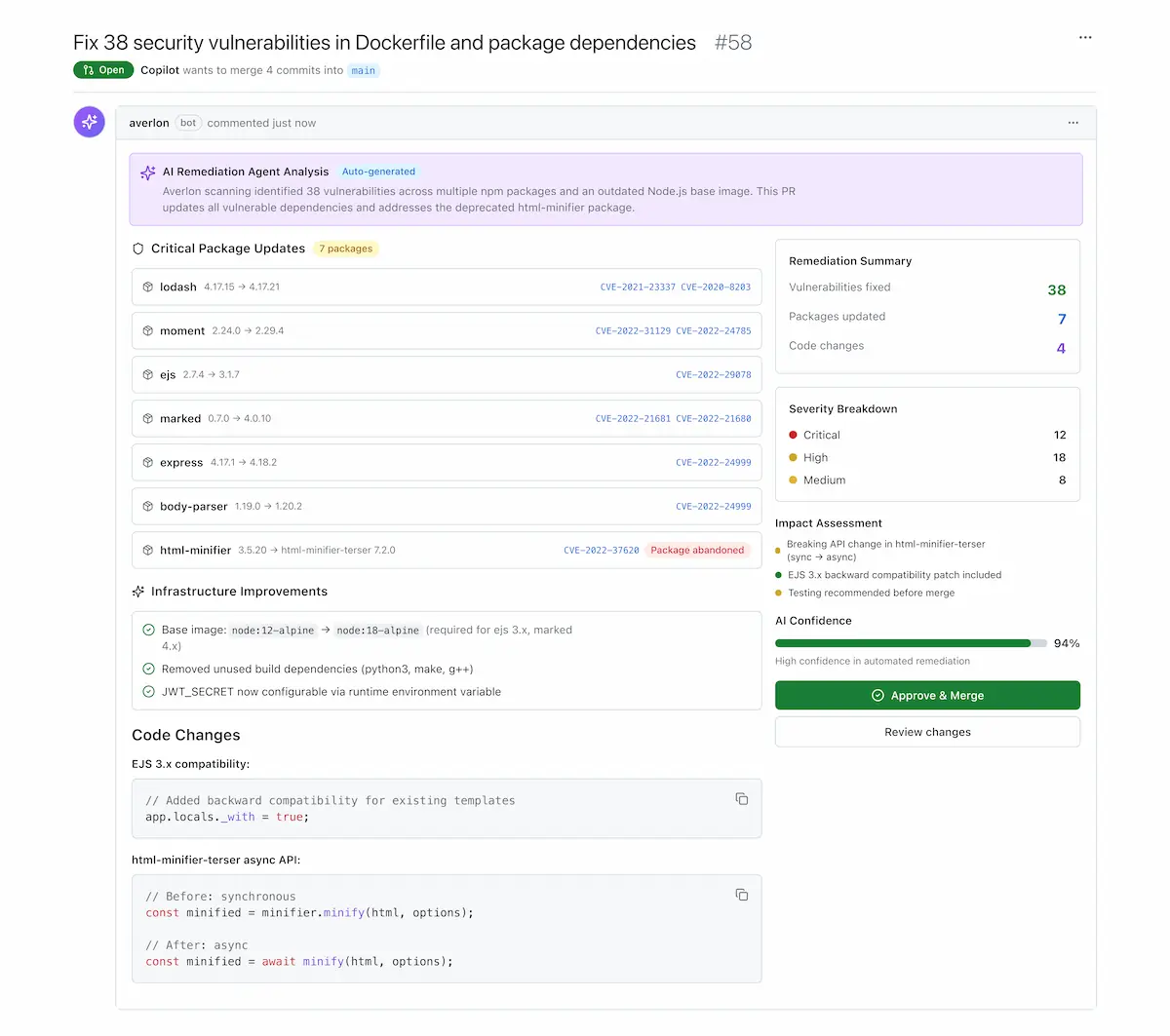
Prevent New Exposure Before It Becomes Backlog
Shrinking backlog isn't enough if new risk keeps entering the system.
Averlon Precog applies the same exploitability and attack-chain reasoning before changes are merged, stopping risk before it reaches production.

Built for Teams Responsible for Reducing Real Exposure
Trusted by Security Leaders
Hear from CISOs and security teams using Averlon to accelerate remediation and reduce risk
"Averlon has saved critical time in our 0-day incident response to issues such as the libWebp vulnerability (CVE-2023-4863). On a steady state basis, we expect it to save our security engineers hundreds of hours per month."


“Averlon surfaces what is truly exploitable in our environment. More importantly, it helps us remediate that risk quickly, which is what ultimately matters.”

"Averlon enables customers to drastically reduce the effort and skill needed in discovering viable Attack Chains… significantly improves the effectiveness of remediations."


"Averlon cut through all the noise and brought attention to what vulnerabilities really matter… Attacks and Mitigations is a language that my board understands."

"Having used several leading vendors’ products, the visibility and insights Averlon provides is unmatched."


"Averlon cuts through the noise and gives my security teams visibility into the vulnerabilities that really matter. Its predictive attack intelligence allows for mitigations before real world attacks materialize."


"With the rise of AI, attacks are becoming more sophisticated. To stay ahead and successfully safeguard their organization, CISOs and their teams must learn how to think like attackers and anticipate how they breach cloud assets. Averlon solves this challenge, providing customers with a holistic way to understand, predict, and prevent cloud security attacks."


"Averlon is a powerful platform that allows enterprises to map exactly how an attacker can compromise an environment. By understanding the attacker’s view, Averlon gives CISOs and their teams unparalleled ability to prioritize what an attacker can explore or exploit to pinpoint threats, predict attacks, and to mitigate them."


Why Exposure Persists
From exploitability and attack chains to remediation gaps and emerging threats, see why identifying risk is easy, but fixing what actually matters remains hard.
Attackers Move Fast. Close the Gap Faster.
Identify what's actually exploitable. Fix it safely. Prevent new risk before it reaches production.







.png)